echo $HISTCONTROL
Start with adding export HISTCONTROL=ignoreboth to your ~/.bashrc right now. Then think about what patterns belong in your HISTIGNORE.
Set HISTCONTROL to ignoredups and Bash will skip any command that matches the one immediately before it:
How Bash Stores Command in History
For example, when you type a command like this, it gets saved in your history.
ignoredups:ignorespace
For example, first, list your bash history.
497 sudo systemctl restart nginx
499 curl https://api.example.com/token
500 ls -la /etc/nginx
export HISTCONTROL=ignoredups
export API_KEY=”supersecretkey123″
Set HISTFILE to /dev/null for the current session:
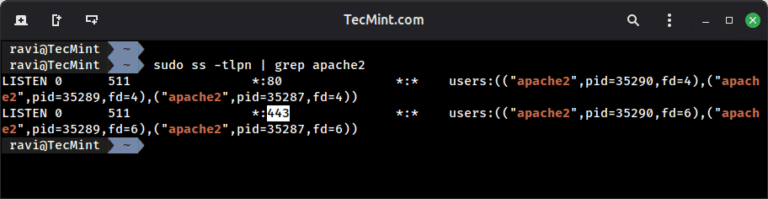
The key variables that govern this behavior live in your shell environment, and you can check them right now:
The good news is that Bash gives you precise control over what it saves, when it saves it, and how to scrub individual entries.
Repeated commands like ls, cd, clear, or git status fill up history fast and make it harder to find the commands you actually care about.
Before you can control history, you need to understand when Bash writes it. For example, during a session, every command goes into an in-memory history list first.
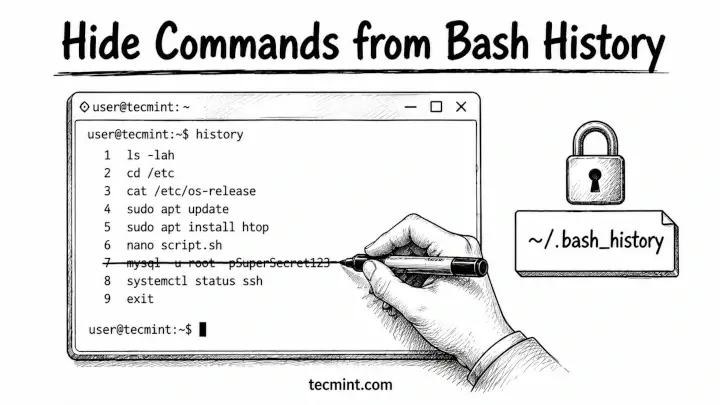
Every Linux user eventually runs a command they’d rather not preserve – a curl with a hardcoded password, an export with an API key, or a one-liner that would confuse any sysadmin who read it three months later. Knowing how to control what ends up in your bash history is as much a security habit as locking down SSH.
history -d 498
To start clean, delete the full history file and remove all past commands.
If you want to scrub the on-disk file immediately without waiting for the session end, run history -w after the deletion:
export HISTIGNORE=”ls:ls -la:cd:pwd:clear:history:exit”
If you’re regularly exporting tokens or running curl with auth headers, those belong there. It takes 5 minutes and saves you from cleaning up sensitive data later.
history -w
history
echo ‘export HISTCONTROL=ignoreboth’ >> ~/.bashrc
source ~/.bashrc
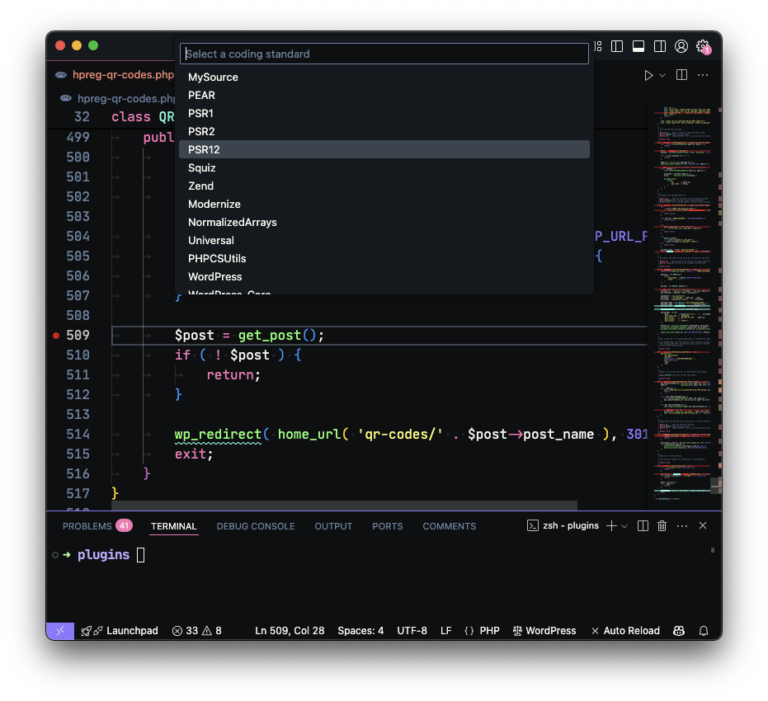
Stop Saving Certain Commands in Bash History
You’ve probably been there: you paste a command with a password embedded, hit Enter, and immediately wonder how many places that string just landed. Bash stores every command you type in ~/.bash_history by default, and on most systems, that file is readable by anyone who can access your account. And if you’re sharing a server with other admins, that history file is the first place anyone looks when something breaks.
source ~/.bashrc
Delete a Specific Command from Bash History
export HISTIGNORE=”ls*:cd*:pwd:clear:history:export *:curl *token*”
You can also combine this with unset HISTFILE if you want to be explicit, but pointing to /dev/null is the more portable approach and works the same way on every distro.
export API_KEY=”supersecretkey123″
So, firt check whether it’s already set:
497 sudo systemctl restart nginx
498 export DB_PASS=”hunter2″
499 curl https://api.example.com/token
500 ls -la /etc/nginx
Have you ever found a password or API key in someone else’s bash history on a shared server? What was the situation and how did you handle it? Tell us in the comments below.
If the variable is empty or missing, add this to your ~/.bashrc:
Most distros default to 1000 in-memory and 2000 on disk, so your file keeps the last 2000 commands across all previous sessions. Understanding that gap between “in memory” and “written to disk” is what makes the next few techniques work cleanly.
Turn Off Command History Temporarily
You now have 5 distinct ways to control bash history: the leading-space trick for one-off sensitive commands, history -d for post-run cleanup, HISTCONTROL for ignoring duplicates and spaces globally, HISTIGNORE for permanent pattern-based exclusions, and HISTFILE=/dev/null for session-wide suppression.
export HISTCONTROL=ignorespace
export HISTFILE=/dev/null
history -c && history -w
history -cclears the in-memory history list for the current session.history -wthen writes that empty list to~/.bash_history, overwriting the file.
Sometimes you want to work on a server without leaving any trace at all such as setting up credentials, auditing a config, or doing incident response on a shared box.
export HISTCONTROL=ignoreboth
The easiest way to stop Bash from saving a command in your history is surprisingly simple, just add a space before the command.
/home/ravi/.bash_history
1000
2000
echo $HISTFILE
echo $HISTSIZE
echo $HISTFILESIZE
When the session ends cleanly, that list gets appended to ~/.bash_history on disk, which matters because if your terminal crashes or you close it with kill, nothing from that session gets saved.